
Stealing All of the Confluence Things
I don’t have to explain to the experienced Red Teamer the treasure trove of secrets and intelligence data that can be found in the pages of an organization's Confluence instance. If the Red Teamer finds herself on a victim’s Confluence site this could mean finding secrets and sensitive data that might lead to an organization’s crown jewels. One might find account passwords, source code, or even private keys and addresses to cloud infrastructure. The victim account might not have access to ALL of the secrets within an organization, but chances are someone misconfigured access rights somewhere and the victim user probably has some unintended access to sensitive Confluence data.
The problem the Red Teamer faces is searching through the large Confluence instance to find the sensitive data that she is in search of. One could use Confluence’s search bar in the interface to search the pages for keywords such as “password,” or “private-key,” but this can take quite a while. There must be a faster and more efficient method, right? Indeed there is.
I developed a Python tool that allows the Red Teamer to use Confluence's API to search through all pages the victim account has access to using an attacker provided keyword list/dictionary to find all pages that contain those keywords. The script then exports all of these pages to PDFs and downloads them to the attacker’s host machine. I call this tool Conf-thief.
The first thing you will need is to compromise a victim’s Confluence instance. I am not going to go into the ways that this can be done, but I will say that I have the most success with this by compromising a target’s Okta account via phishing and using an Evilginx2 Machine-in-the-Middle (MITM) server to create a fake Okta page. I explain this attack path in greater detail here.
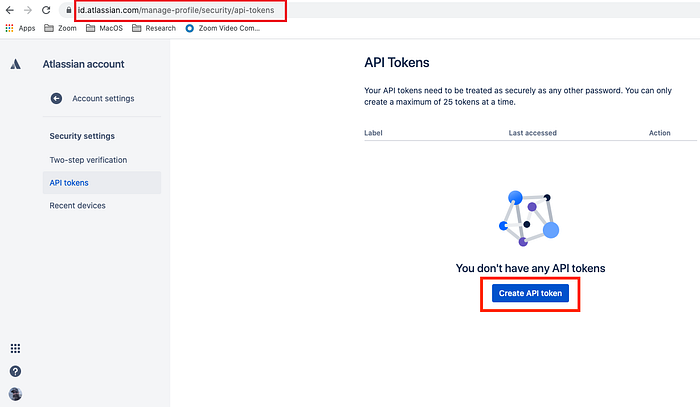
Once one has compromised a Confluence page, one will need to activate and steal the victim’s Confluence API key. This is a simple process. While logged in to the victim’s Okta account, simply navigate to https://id.atlassian.com/manage-profile/security/api-tokens and click the “Create API Token” button.
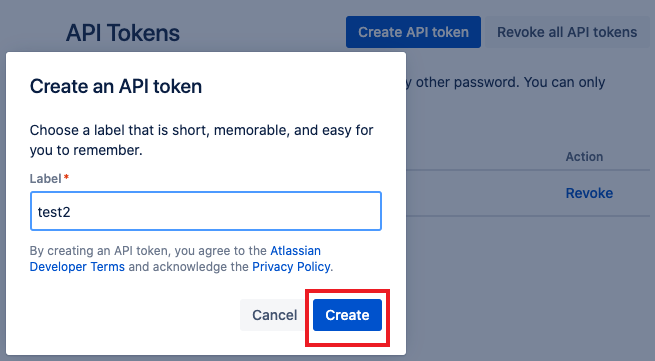
Next, one will need to give it a name/label. It is best to use something inconspicuous. Then click the “Create” button.
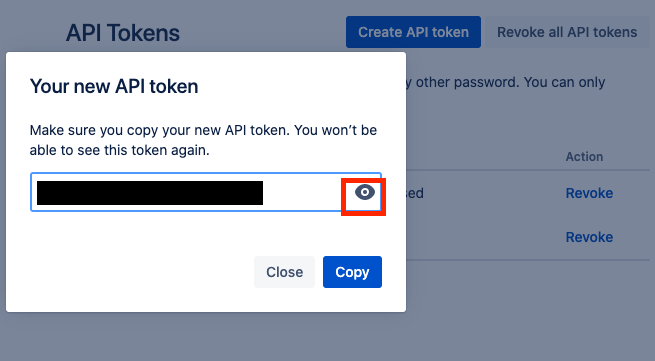
Now one will be given an API Token. Click the eyeball icon if one wants to see it. Make sure one copies it and holds on to it. One will need it to run Conf-Thief. Creating this token will probably send an email to the victim, but that hasn’t been a problem for me yet.
Now that one has the API token one needs one final piece of information: The victim’s username. This is just the email address of the victim. One can find this on the victim’s Confluence “Profile and Visibility” page if one doesn’t already have it for whatever reason.
Now one just needs to download Conf-thief from my github here, run
pip install atlassian-python-api , and run the script using the Confluence URL, username and API key for the victim that one just stole.
python3 conf_thief.py [-h] -c <TARGET URL> -u <Target Username> -p <API ACCESS TOKEN> -d <DICTIONARY FILE PATH>That’s it. One can use the keyword list I have provided via SecLists secrets-keywords.txt, or use one’s own to allow Conf-thief to search for the confluence pages for the keywords one wishes to find in the pages. Depending on the size of the Confluence instance, and the pages the victim has access to, this search can take a long time. The exporting of the pages to PDF and the downloading could take even longer, so one might want to start with a shorter, custom dictionary.
Wrapping up
Hopefully this tool comes in handy for you on your next Red Team operation. I know it will for mine. Let me know if you have any more functionality ideas for this, or fork my repo and request a pull. I need to add threading to make the exporting and downloading go faster.
As always, thanks for reading!
